Spanning Tree Protocol (STP) and Rapid Spanning Tree Protocol (RSTP) are switching mechanisms that prevent a LAN with redundant links to forward Ethernet frames to loop in an indefinite time in a network. STP and RSTP have features that help the network work better and more securely, such as Portfast, BPDU Guard, and Root Guard.
What is a Bridge Protocol Data Unit (BPDU)?
A bridge protocol data unit (BPDU) is a data message forwarded across a Local Area Network (LAN) to detect loops in a spanning tree topology. A BPDU contains information about ports, switches, port priority, and addresses.
PortFast
PortFast enables the switch to instantaneously transition from blocking state to forwarding state immediately through bypassing the listening and learning state. However, PortFast is highly recommended only on non-trunking access ports, such as edge ports, because these ports typically do not send nor receive BPDU.
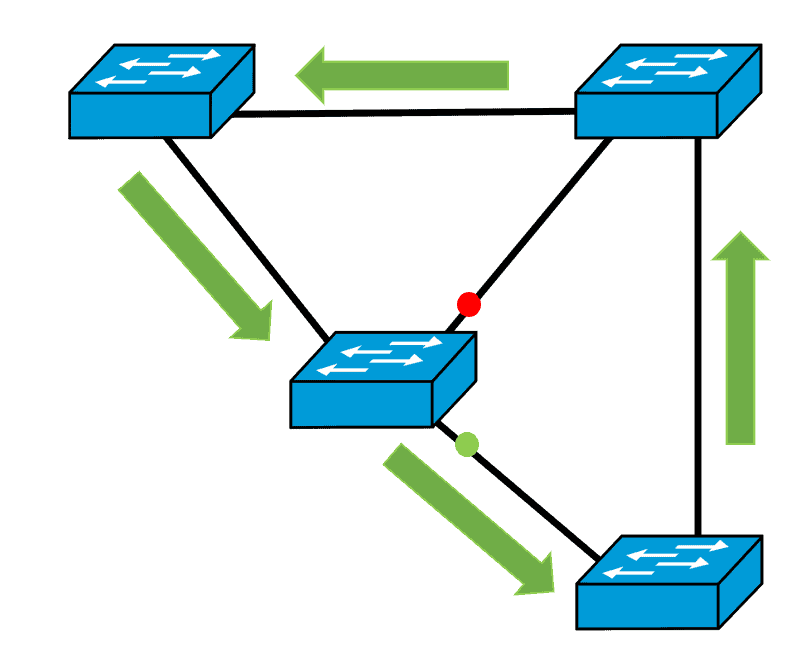
It is advisable to implement PortFast only on edge ports that connect end stations to the switches, similar to the example STP topology below.
Configuring PortFast on an Access Port
We can configure the PortFast command on an access switch port interface. See the configuration example below:
Sw1(config)# interface f0/10 Sw1(config-if)# spanning-tree portfast Sw1(config)# spanning-tree portfast default
BPDU Guard
Because PortFast can be enabled on non-trunking ports connecting two switches, spanning-tree loops can occur because Bridge Protocol Data Units (BPDUs) are still being transmitted and received on those ports.
Layer 2 loops in our network topology can be prevented by enabling another feature called PortFast BPDU Guard wherein it prevents the loop from happening by moving non-trunking switch ports into an errdisable state when the Bridge Protocol Data Unit (BPDU) is accepted on that port. Whenever STP BPDU guard is enabled on the switch, STP shuts down PortFast-configured interfaces on the switch that received Bridge Protocol Data Unit (BPDU) instead of putting them into STP blocking state.
In a correct configuration, PortFast-configured ports do not receive BPDU. If a PortFast-configured interface receives a Bridge Protocol Data Unit (BPDU), a misconfiguration exists. BPDU guard provides a secure response to invalid configurations because the network engineer needs to manually put the interface in a forwarding state.
Enabling BPDU Guard
We enable the BPDU guard command in the interface configuration mode. This configuration example shows how to configure BPDU guard in Switch1’s FastEthernet0/1 interface.
Switch1(config)# interface fastethernet0/1 Switch1(config-if)# spanning-tree portfast Switch1(config-if)# spanning-tree bpduguard enable Switch1(config)# spanning-tree portfast bpduguard default
Root Guard
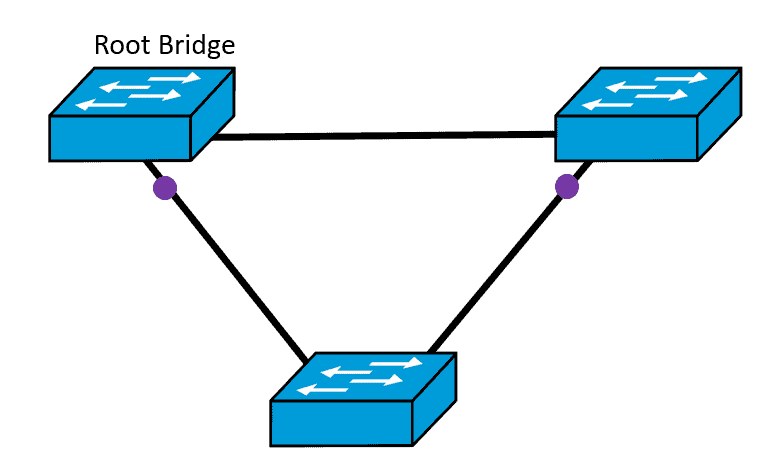
Any switch in the network can be designated as the root bridge. But to efficiently forward frames, the positioning of the root bridge should be predetermined in a strategic location. The standard STP does not ensure that the root bridge can be assigned permanently by the administrator.
An enhanced feature of STP is developed to address this issue. The root guard feature enables a way to implement the root bridge deployment in the network.
The root guard assures that the interface on which the root guard is enabled is set as the designated port. Normally, the root bridge ports are all set as designated ports unless two or more root bridge ports are connected. If the bridge receives superior STP Bridge Protocol Data Units (BPDUs) on a root guard-enabled interface, the root guard moves this interface to a root-inconsistent STP state. This root-inconsistent state is effectively equivalent to a listening state. No traffic is forwarded across this interface. In this process, the root guard enforces the position of the root bridge.
Configuring Root Guard
Configuration on the interface level of root guard for Catalyst 6500/6000 and Catalyst 4500/4000 are shown below:
Switch# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Switch#(config)# interface fastethernet 3/1 Switch#(config-if)# spanning-tree guard root
On the Cisco Switches Catalyst 2900XL, 3500XL, 2950, and 3550, we configure root guard as shown:
Switch# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Switch(config)# interface fastethernet 0/8 Switch(config-if)# spanning-tree rootguard
Download our Free CCNA Study Guide PDF for complete notes on all the CCNA 200-301 exam topics in one book.
We recommend the Cisco CCNA Gold Bootcamp as your main CCNA training course. It’s the highest rated Cisco course online with an average rating of 4.8 from over 30,000 public reviews and is the gold standard in CCNA training: