Unlike with static NAT, where you had to manually define a static mapping between a private and public address, dynamic NAT does the mapping of a local address to a global address happens dynamically. This means that the router dynamically picks an address from the global address pool that is not currently assigned. The dynamic entry stays in the NAT translations table as long as the traffic is exchanged. The entry times out after a period of inactivity and the global IP address can be used for new translations.
With dynamic NAT, you need to specify two sets of addresses on your Cisco router:
- the inside addresses that will be translated
- a pool of global addresses
To configure dynamic NAT, the following steps are required:
1. configure the router’s inside interface using the ip nat inside command
2. configure the router’s outside interface using the ip nat outside command
3. configure an ACL that has a list of the inside source addresses that will be translated
4. configure a pool of global IP addresses using the ip nat pool NAME FIRST_IP_ADDRESS LAST_IP_ADDRESS netmask SUBNET_MASK command
5. enable dynamic NAT with the ip nat inside source list ACL_NUMBER pool NAME global configuration command
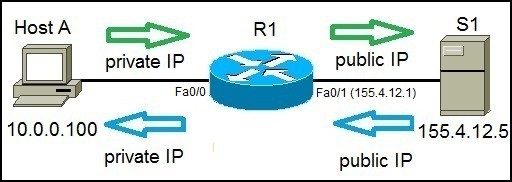
Consider the following example:
Host A requests a web resource from a internet server S1. Host A uses its private IP address when sending the request to router R1. Router R1 receives the request, changes the private IP address to one of the available global addresses in the pool and sends the request to S1. S1 responds to R1. R1 receives the response, looks up in its NAT table and changes the destination IP address to the private IP address of Host A.
To configure dynamic NAT, the following commands are required on R1:
1. First we need to configure the router’s inside and outside NAT interfaces:
R1(config)#int f0/0 R1(config-if)#ip nat inside R1(config-if)#int f0/1 R1(config-if)#ip nat outside
2. Next, we need to configure an ACL that will include a list of the inside source addresses that will be translated. In this example we want to translate all inside hosts on the 10.0.0.0/24 network:
R1(config)#access-list 1 permit 10.0.0.0 0.0.0.255
3. We need to configure the pool of global (public) IP addresses available on the outside interface:
R1(config)#ip nat pool STUDY-CCNA_POOL 155.4.12.1 155.4.12.3 netmask 255.255.255.0
The pool configured above consists of 3 addresses: 155.4.12.1, 155.4.12.2, and 155.4.12.3.
4. Lastly, we need to enable dynamic NAT:
R1(config)#ip nat inside source list 1 pool STUDY-CCNA_POOL
The command above tells the router to translate all addresses specified in the access list 1 to the pool of global addresses named MY POOL.
You can list all NAT translations using the show ip nat translations command.
Generate some traffic from the PC to the server first to test:
C:\>ping 155.4.12.5
Pinging 155.4.12.5 with 32 bytes of data:
Reply from 155.4.12.5: bytes=32 time<1ms TTL=127
Reply from 155.4.12.5: bytes=32 time=3ms TTL=127
Reply from 155.4.12.5: bytes=32 time=1ms TTL=127
Reply from 155.4.12.5: bytes=32 time<1ms TTL=127
Ping statistics for 155.4.12.5:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 0ms, Maximum = 3ms, Average = 1ms
Then enter the show ip nat translations command quickly enough before the translation has timed out:
R1#show ip nat translations Pro Inside global Inside local Outside local Outside global icmp 155.4.12.1:16 10.0.0.100:16 155.4.12.5:16 155.4.12.5:16
In the output above you can see that the translation has been made between the Host A’s private IP address (Inside local, 10.0.0.100) to the first available public IP address from the pool (Inside global, 155.4.12.1) and it is connecting to the server on the outside (Outside local and Outside global, 155.4.12.5) .
You can remove all NAT translations from the table by using the clear ip nat translation * command.
Download our Free CCNA Study Guide PDF for complete notes on all the CCNA 200-301 exam topics in one book.
We recommend the Cisco CCNA Gold Bootcamp as your main CCNA training course. It’s the highest rated Cisco course online with an average rating of 4.8 from over 30,000 public reviews and is the gold standard in CCNA training: