By default, all interfaces on a Cisco switch are turned on. That means that an attacker could connect to your network through a wall socket and potentially threaten your network. If you know which devices will be connected to which ports, you can use the Cisco security feature called port security. By using port security, a network administrator can associate specific MAC addresses with the interface, which can prevent an attacker to connect his device. This way you can restrict access to an interface so that only the authorized devices can use it. If an unauthorized device is connected, you can decide what action the switch will take, for example discarding the traffic and shutting down the port.
To configure port security, three steps are required:
1. define the interface as an access interface by using the switchport mode access interface subcommand
2. enable port security by using the switchport port-security interface subcommand
3. define which MAC addresses are allowed to send frames through this interface by using the switchport port-security mac-address MAC_ADDRESS interface subcommand or using the swichport port-security mac-address sticky interface subcommand to dynamically learn the MAC address of the currently connected host
Two steps are optional:
1. define what action the switch will take when receiving a frame from an unauthorized device by using the port security violation {protect | restrict | shutdown} interface subcommand. All three options discard the traffic from the unauthorized device. The restrict and shutdown options send log messages when a violation occurs. Shut down mode also shuts down the port.
2. define the maximum number of MAC addresses that can be used on the port by using the switchport port-security maximum NUMBER interface submode command
The following example shows the configuration of port security on a Cisco switch:
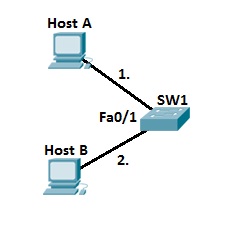
First, we need to enable port security and define which MAC addresses are allowed to send frames:
SW1(config)#interface fastEthernet0/1 SW1(config-if)#switchport mode access SW1(config-if)#switchport port-security SW1(config-if)#switchport port-security mac-address sticky
Next, by using the show port-security interface fa0/1 we can see that the switch has learned the MAC address of host A:
SW1#show port-security interface fastEthernet0/1 Port Security : Enabled Port Status : Secure-up Violation Mode : Shutdown Aging Time : 0 mins Aging Type : Absolute SecureStatic Address Aging : Disabled Maximum MAC Addresses : 1 Total MAC Addresses : 1 Configured MAC Addresses : 0 Sticky MAC Addresses : 1 Last Source Address:Vlan : 000A.4188.D0C3:1 Security Violation Count : 0
By default, the maximum number of allowed MAC addresses is one, so if we connect another host to the same port, the security violation will occur:
SW1#show interfaces fastEthernet0/1 FastEthernet0/1 is down, line protocol is down (err-disabled) Hardware is Lance, address is 0001.c79a.4501 (bia 0001.c79a.4501) BW 100000 Kbit, DLY 1000 usec, reliability 255/255, txload 1/255, rxload 1/255
The status code of err-disabled means that the security violation occurred on the port.
To enable the port, we need to use the shutdown and no shutdown interface subcommands.
Download our Free CCNA Study Guide PDF for complete notes on all the CCNA 200-301 exam topics in one book.
We recommend the Cisco CCNA Gold Bootcamp as your main CCNA training course. It’s the highest rated Cisco course online with an average rating of 4.8 from over 30,000 public reviews and is the gold standard in CCNA training:
