To create an standard access list on a Cisco router, the following command is used from the router’s global configuration mode:
R1(config)# access-list ACL_NUMBER permit|deny IP_ADDRESS WILDCARD_MASK
ACL number for the standard ACLs has to be between 1–99 and 1300–1999.
You can also use the host keyword to specify the host you want to permit or deny:
R1(config)# access-list ACL_NUMBER permit|deny host IP_ADDRESS
Once the access list is created, it needs to be applied to an interface. You do that by using the ip access-group ACL_NUMBER in|out interface subcommand. in and out keywords specify in which direction you are activating the ACL. in means that ACL is applied to the traffic coming into the interface, while the out keyword means that the ACL is applied to the traffic leaving the interface.
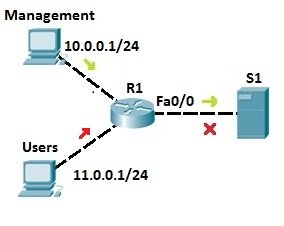
Consider the following network topology:
We want to allow traffic from the management LAN to the server S1. First, we need to write an ACL to permit traffic from LAN 10.0.0.0/24 to S1. We can use the following command on R1:
R1(config)#access-list 1 permit 10.0.0.0 0.0.0.255
The command above permits traffic from all IP addresses that begin with 10.0.0. We could also target the specific host by using the host keyword:
R1(config)#access-list 1 permit host 10.0.0.1
The command above permits traffic only from the host with the IP address of 10.0.0.1.
Next, we will deny traffic from the Users LAN (11.0.0.0/24):
R1(config)#access-list 1 deny 11.0.0.0 0.0.0.255
Next, we need to apply the access list to an interface. It is recommended to place the standard access lists as close to the destination as possible. In our case, this is the Fa0/0 interface on R1. Since we want to evaluate all packets trying to exit out Fa0/0, we will specify the outbound direction with the out keyword:
R1(config-if)#ip access-group 1 out
At the end of each ACL there is an implicit deny all statement. This means that all traffic not specified in earlier ACL statements will be forbidden, so the second ACL statement (access-list 1 deny 11.0.0.0 0.0.0.255) wasn’t even necessary.
Download our Free CCNA Study Guide PDF for complete notes on all the CCNA 200-301 exam topics in one book.
We recommend the Cisco CCNA Gold Bootcamp as your main CCNA training course. It’s the highest rated Cisco course online with an average rating of 4.8 from over 30,000 public reviews and is the gold standard in CCNA training: