This article will discuss the differences between network security devices – firewalls, Intrusion Prevention Systems (IPS), and Intrusion Detection Systems (IDS). The major distinction is that a firewall blocks and filters network traffic, but an IDS/IPS detects and alerts an administrator or prevents the attack, depending on the setup.
A firewall permits traffic depending on a set of rules that have been set up. It is based on the source, destination, and port addresses. A firewall can deny any traffic that does not satisfy the specified criteria. IDS are passive monitoring system devices that monitor network traffic as they travel over the network, compare signature patterns, and raise an alarm if suspicious activity or known security threat is detected. On the other hand, IPS is an active device that prevents attacks by blocking them.
Firewalls
A firewall employs rules to filter incoming and outgoing network traffic. It uses IP addresses and port numbers to filter traffic. It can be set to either Layer 3 or transparent mode. The firewall should be the first line of defense and installed inline at the network’s perimeter.
There are also different types of firewalls like proxy firewall, stateful inspection firewall, unified threat management (UTM) firewall, next-generation firewall (NGFW), threat-focused NGFW, and a virtual firewall.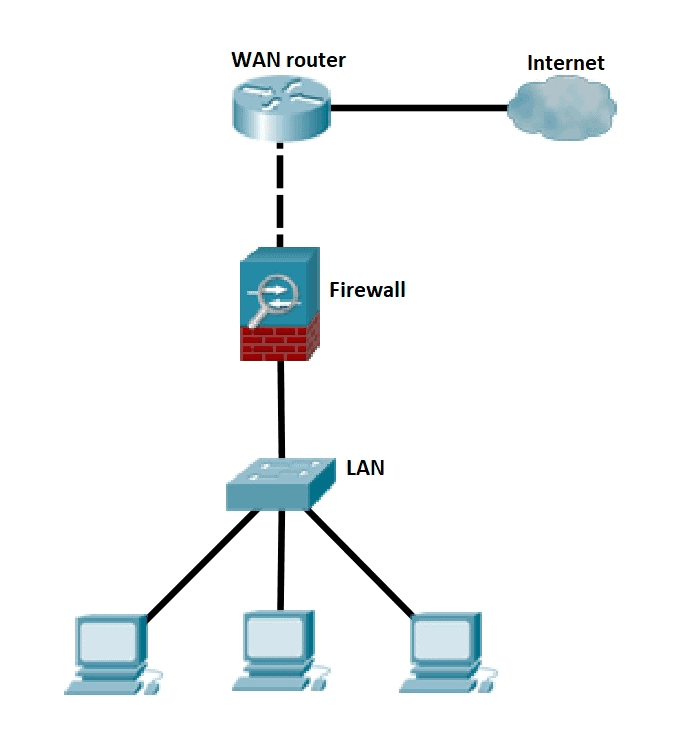
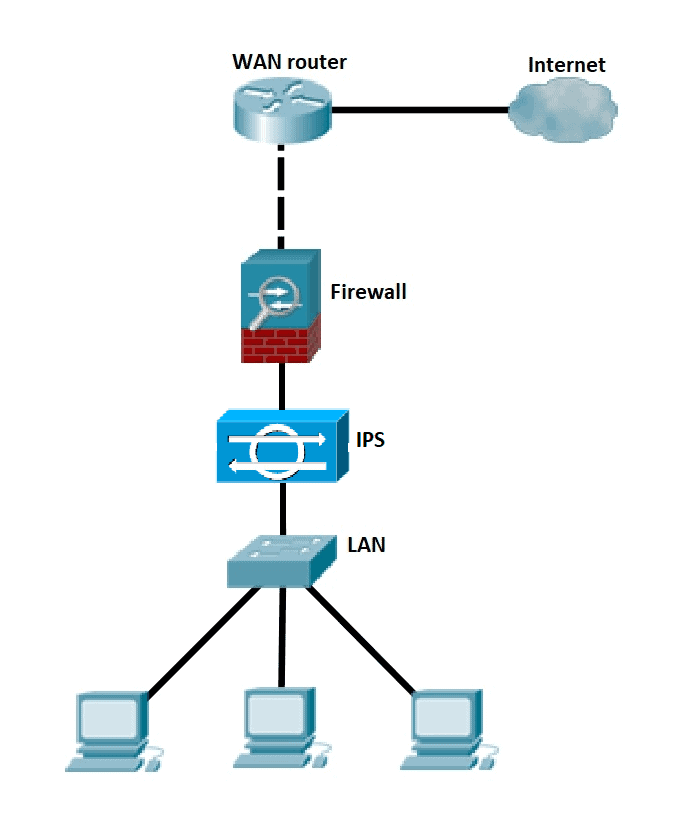
Intrusion Prevention System (IPS)
IPS is a device that inspects, detects, classifies, and proactively prevents harmful traffic. It examines real-time communications for attack patterns or signatures and then blocks attacks when they have been detected. Placement and configuration in inline mode and generally being in Layer 2 after the firewall. In inline mode, traffic passes into one of the device’s ethernet ports and out of the other.
Intrusion Prevention System must work efficiently to avoid decreasing network performance. It must be quick because exploits might occur anytime. To eliminate threats and false positives, the IPS must detect and respond accurately.
Some of the actions of IPS include:
- Alerting network administrators (anomaly-based detection)
- Dropping the malicious traffic
- Denying traffic from the source address
- Reset the connection
Intrusion Detection System (IDS)
IDS is either a hardware or software program that analyzes incoming network traffic for malicious activities or policy breaches (network behavior analysis) and issues alerts when they are detected. It detects real-time traffic and searches for attack signatures or traffic patterns, then sends out alarms. Unlike IPS, a network Intrusion Detection System is not in line with the data path, so it can only alert and alarm on detection of anomalies.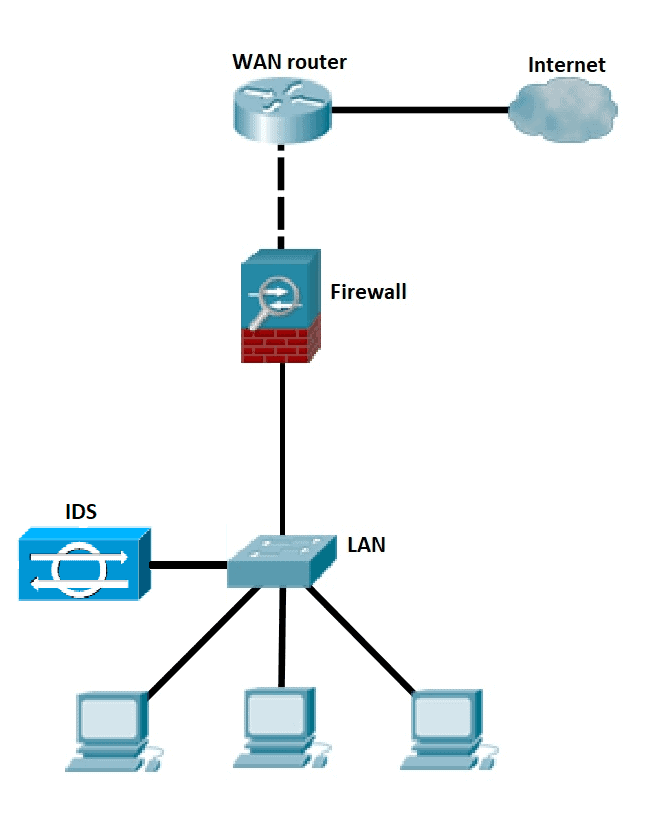
Download our Free CCNA Study Guide PDF for complete notes on all the CCNA 200-301 exam topics in one book.
We recommend the Cisco CCNA Gold Bootcamp as your main CCNA training course. It’s the highest rated Cisco course online with an average rating of 4.8 from over 30,000 public reviews and is the gold standard in CCNA training: